wordlist is just a list of words that aircrack-ng is going to go through, and trying each one against the handshake until it successfully determines the WPA key. If the wordlist is better, the chances of cracking the WPA key will be higher. If the password is not in our wordlist file, we will not be able to determine the WPA key.
To create the wordlist, we're going to use a tool called crunch. The syntax is as follows:
where
- crunch is the name of the tool.
- [min] specifies the minimum number of characters for the password to be generated.
- [max] specifies the maximum number of characters for the password.
- characters specify the characters that we want to use in the password. For example, you can put all lowercase characters, all uppercase characters, numbers, and symbols.
- -t is optional. It specifies the pattern.
- -o option specifies the filename where the passwords are going to be stored.
If we know the part of the password, -t option is very useful. For example: if we're trying to guess the password of someone and we have seen him typing the password, we know that the password starts with a and end with b. Now we can use the pattern option and tell crunch to create passwords that always start with a and end with b and put all possible combinations of the characters that we put in the command.
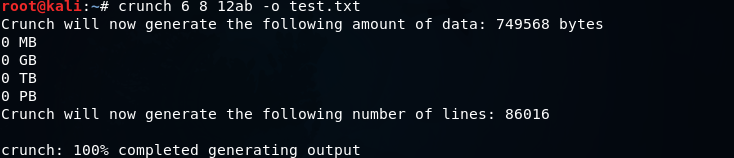
We're going to use crunch, and then we're going to make a minimum of 6 and maximum of 8. We're going to put 12ab, and store it in test.txt. The crunch is going to create a combination of passwords (minimum of 6 characters and maximum of 8 characters), and it's going to create all possible combination of 12ab. It's going to store all the combination in a file called test.txt. The command will be as follows:

The following output will be shown after executing the above command:
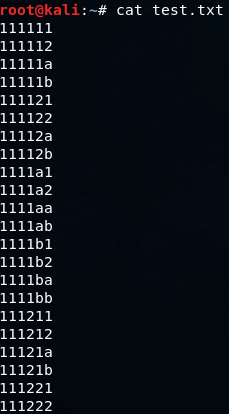
Using cat test.txt command, we can see all of the passwords that are stored in the file test.txt. The following screenshot shows all the passwords:
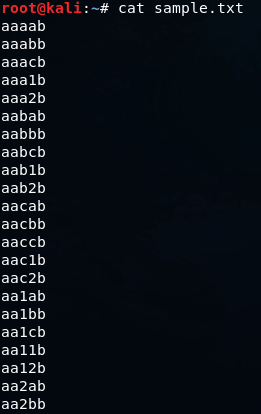
Now let's take a look at the pattern option. We will go to crunch, using a minimum of 5 and maximum of 5, so all password will be five characters long. Then we will put the characters, which are abc12 and we will add the -t option, which is the pattern option, then we will put a@@@b that means the password starts with an a and end with b. Through this, we will get all possible combination of characters between a and b. Then, we are going to specify the output file -o, let's call it sample.txt. The command will be as follows:
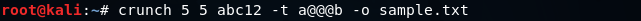
The output will be as follows:
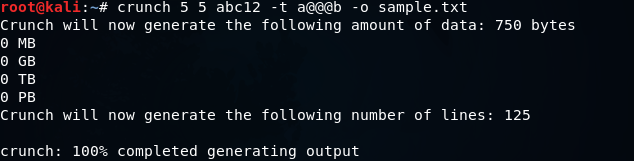
It creates 125 passwords. Now let's take a look at them. In the following screenshot, we can see that they always start with an a and always end with b.